Reverse Engineering Your Gadgets: Why Developers Are Starting to Care
March 1, 2026
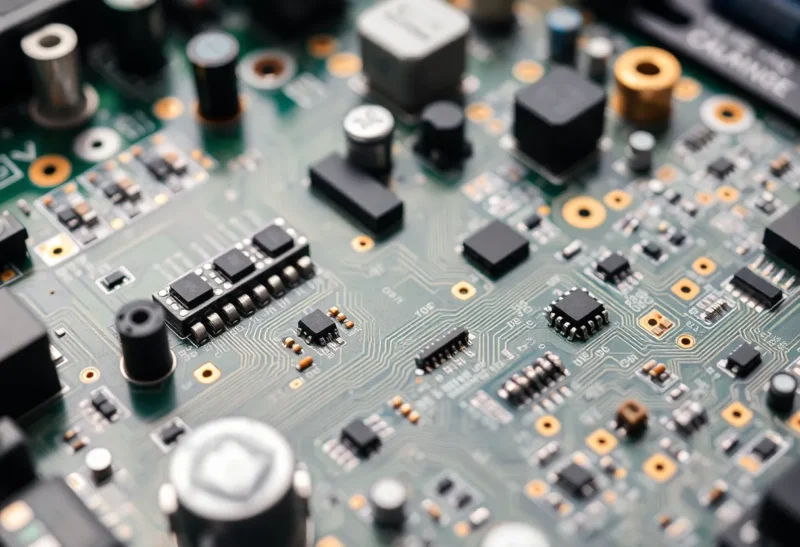
Reverse engineering used to be the domain of hardware hackers and security researchers. Tear down a gadget, trace the circuit, dump the firmware—see what makes it tick. Most software developers stayed away. It was niche, legally murky, and frankly intimidating. But that’s changing. Right-to-repair laws are rolling out. Open-source hardware and firmware projects are growing. And developers are discovering that understanding how their devices work—and how to modify them—is increasingly valuable. Here’s why reverse engineering is going mainstream, what developers are learning from it, and how to get started without ending up in legal trouble.
What Changed
For years, manufacturers treated their gadgets as black boxes. Proprietary firmware, locked bootloaders, no schematics. If it broke, you replaced it. If you wanted to modify it, you were on your own—and possibly violating terms of service or the DMCA. But the landscape has shifted.
Right-to-repair laws in the EU and several US states require manufacturers to provide parts, tools, and documentation for certain products. That doesn’t mandate reverse engineering, but it normalizes the idea that users have a right to understand and fix what they own. Meanwhile, open-source firmware projects—from router firmware to smart home hubs—have proven that community-led reverse engineering can produce viable alternatives. Developers who contribute to or use these projects are increasingly comfortable poking under the hood.
At the same time, the DMCA’s anti-circumvention provisions have come under pressure. Exemptions for security research, interoperability, and repair have expanded. That doesn’t make everything legal—but it clarifies that reverse engineering for legitimate purposes is increasingly protected. The legal fog is lifting, and developers are stepping in.

Why Developers Care Now
First, interoperability. As devices multiply—smart home, wearables, IoT—developers need to integrate them. APIs are often limited, undocumented, or absent. Reverse engineering reveals how a device communicates, what protocols it uses, and how to talk to it. A developer building a home automation system might need to reverse engineer a thermostat to add local control. A fitness app might need to decode a wearable’s data format. It’s not malicious—it’s practical.
Second, security. Understanding how a device works is the first step to securing it. Researchers routinely reverse engineer firmware to find vulnerabilities. Bug bounty programs and responsible disclosure depend on people who can tear things apart. Developers who learn reverse engineering contribute to a safer ecosystem.
Third, sustainability and repair. When a device breaks, reverse engineering can reveal why—and how to fix it. Schematics, part numbers, and firmware dumps help repair shops and DIYers extend product life. Developers who care about e-waste and right-to-repair are increasingly involved in projects that document and repair gadgets.
Fourth, learning. Reverse engineering is a crash course in embedded systems, communication protocols, and low-level software. For developers who normally work in high-level languages, it’s a window into how the hardware actually behaves. That knowledge transfers: debugging becomes easier, architecture decisions become clearer, and the gap between “code” and “metal” narrows.

How to Start (Without Getting in Trouble)
First, choose your target wisely. Start with devices that have existing documentation or community support. Routers running OpenWrt, smart plugs with Tasmota, gadgets with known-good teardowns—these are low-risk entry points. Avoid products with aggressive legal teams or unclear ownership. When in doubt, research first.
Second, document your intent. Reverse engineering for interoperability, security research, or repair is generally defensible. Reverse engineering to copy proprietary code or bypass licensing is not. Know the difference. Keep notes. If you publish findings, frame them as research or interoperability—not as a how-to for piracy.
Third, use the right tools. Logic analyzers, oscilloscopes, and JTAG debuggers for hardware. Ghidra, IDA, and binary ninja for firmware. Wireshark for network traffic. The learning curve is steep, but the tooling is mature. Start with software—firmware dumps, protocol analysis—before investing in hardware.
Fourth, join communities. iFixit, Hackaday, and project-specific forums (OpenWrt, Tasmota, etc.) are full of people who’ve reverse engineered similar devices. Ask questions. Share findings. The culture is collaborative, and the collective knowledge is vast.
The Bottom Line
Reverse engineering is going mainstream. Developers are using it for interoperability, security, repair, and learning. The legal and cultural barriers are lower than they’ve been in years. If you’ve ever wanted to understand how your gadgets work—or how to make them work better—now is a good time to start. Pick a device with community support, learn the tools, and contribute back. The right-to-repair movement needs people who can read the code. Be one of them.








