Why Your EV’s Over-the-Air Updates Could Be a Security Risk
February 24, 2026

Over-the-air updates have turned your car into a upgradable device. Bug fixes, new features, and performance tweaks arrive without a trip to the dealer. That’s convenient—and it’s also a new attack surface. Every OTA pipeline is a path from the internet to the computers that control your brakes, steering, and battery. When that path isn’t designed and defended with security first, your EV can become a target. Here’s why OTA updates are a security risk, and what to look for when you’re in the market.
The Appeal of OTA
OTA updates are a win for manufacturers and many owners. Carmakers can fix software bugs and roll out improvements without recalling vehicles. Owners get new features and fixes without scheduling service. The model is borrowed from phones and laptops: the product gets better over time. For EVs, where software controls everything from range estimation to battery management, that flexibility is especially valuable.
But a car isn’t a phone. Compromise a phone and you lose data or get defrauded. Compromise a car and the stakes can be physical. That doesn’t mean OTA is inherently bad—it means the security of the update pipeline and the vehicle’s software architecture has to be taken seriously.
Where the Risks Come From
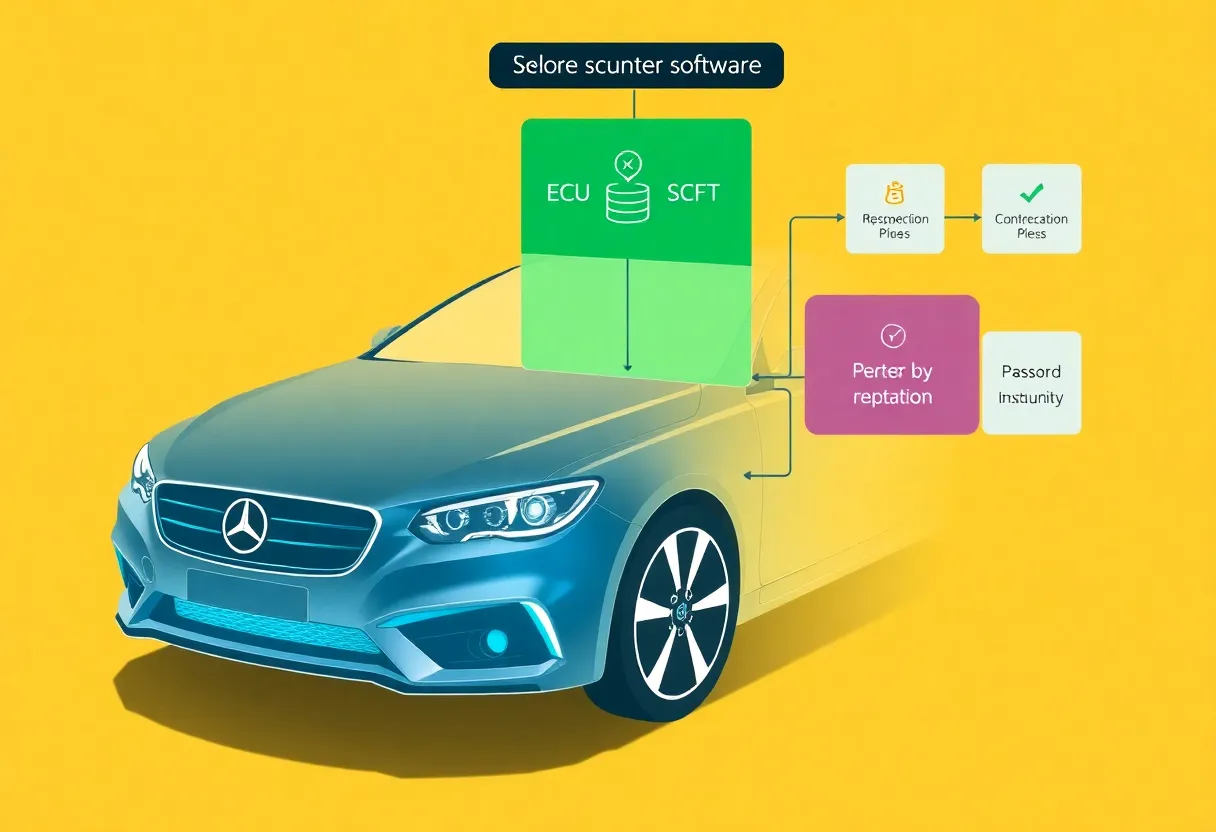
Compromised update channel. If an attacker can push malicious or tampered firmware through the same channel the manufacturer uses, they can gain control over vehicle systems. That requires breaching the manufacturer’s backend or intercepting and modifying updates in transit. It’s not trivial—but it’s the nightmare scenario, and it’s why update signing, secure delivery, and integrity checks are non-negotiable.
Vulnerable update process. Even when the update itself is legitimate, the process of installing it can have flaws. Can an update be forced or triggered under the right conditions? Are there weak points in how the car verifies and applies new software? Researchers have repeatedly found vulnerabilities in automotive update and diagnostic interfaces.
Overconnected architecture. If the same network path that receives OTA updates can reach safety-critical ECUs without strong isolation, one compromise can spread. Modern vehicles have dozens of computers. Segmentation—so that infotainment and OTA don’t have unfettered access to braking or steering—is essential. Not every platform gets it right.
Supply chain and vendor trust. Carmakers don’t write every line of code. They rely on tier-one suppliers and software partners. A vulnerability in a component or in the build pipeline can ship to millions of vehicles. You’re trusting a long chain; every link matters.
What Good Looks Like
Secure OTA isn’t impossible. It requires: cryptographically signed updates so only the manufacturer can push valid firmware; secure boot so the car only runs software that’s been verified; network segmentation so the OTA and connectivity stack can’t directly command safety-critical systems; and a process for responding to vulnerabilities when researchers or attackers find them. Some manufacturers are investing heavily in this. Others are still catching up. As a buyer or owner, you can’t audit the code—but you can ask whether the brand has a published security program, a bug bounty, and a track record of timely patches.
The Bottom Line
OTA updates make your EV more capable and often safer—when the pipeline itself is secure. The risk isn’t OTA itself; it’s OTA done poorly. The industry is moving toward better practices, but not every vehicle is there yet. When you’re shopping or when you’re waiting for the next update to land, it’s worth remembering: that convenience comes with a responsibility to build and defend the update channel right. Your car is now a connected device. Treat it like one.