
For decades, security was built around the castle-and-moat idea: hard perimeter, trusted inside. Once you were on the network, you could reach most of what you needed. That model is falling apart. Work is remote, apps live in the cloud, and the “inside” of the network is no longer a safe place to assume trust. Zero-trust security flips the script: never trust, always verify. Every access request is checked, regardless of where it comes from. Here’s what zero-trust is, why it matters, and why you’ll need it sooner or later.
What Zero-Trust Actually Means
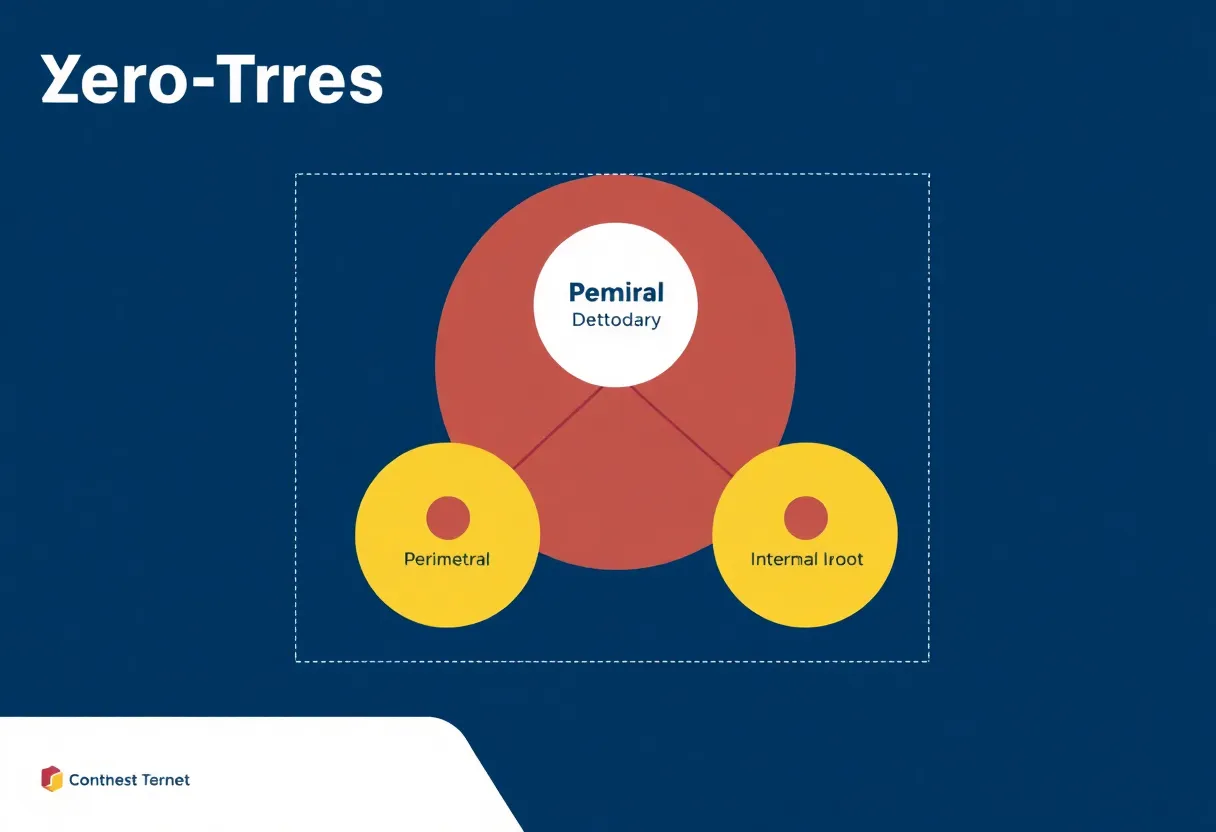
Zero-trust isn’t a single product or protocol. It’s a set of principles: verify explicitly, use least-privilege access, and assume breach. In practice, that means:
- Identity is the new perimeter. Instead of “you’re on the VPN, so you’re trusted,” every request is tied to a user or device identity that’s checked against policy. No default trust based on network location.
- Least privilege. Users and services get only the access they need for a specific task, for as long as they need it. No broad, standing access to whole segments of the network.
- Assume breach. Design so that if an attacker gets in (or is already inside), they can’t easily move laterally. Segment resources, encrypt in transit and at rest, and log and monitor so that anomalous access is visible.
Zero-trust doesn’t require you to rip out everything and start over. It’s a direction of travel: add identity-aware access controls, tighten segmentation, and reduce implicit trust step by step.

Why the Old Model Is Failing
Traditional security assumed a clear inside and outside. Firewalls and VPNs protected the perimeter; once you were in, you could reach internal apps and data. But today, “inside” is fuzzy. Employees work from home, coffee shops, and partner networks. Applications run in public clouds and SaaS. Data lives in a dozen services. The perimeter has effectively dissolved. A VPN only proves you’re allowed to be on the VPN—it doesn’t prove who you are or what you should see. Attackers who steal credentials or compromise a device can ride that “trusted” access straight into the heart of the network.
Zero-trust addresses that by making every access decision explicit. Want to open this app? Prove who you are (and that your device is healthy). Want to reach this database? Your role and context are checked again. There’s no single “you’re in” moment; there are many small checks. That makes it harder for an attacker to move from one compromise to full access.
What You Need to Get Started
Implementing zero-trust usually involves a mix of identity, network, and endpoint controls. Strong identity and multi-factor authentication (ideally phishing-resistant, like passkeys) are the foundation. Then you add:
- Identity-aware access. A policy engine that grants or denies access to applications and data based on user, device, and context (e.g. “only from managed device, from this country, at this time”).
- Micro-segmentation. Dividing the network or application layer so that workloads can’t talk to each other unless explicitly allowed. That limits lateral movement.
- Endpoint visibility. Knowing what devices are connecting, whether they’re compliant (patched, encrypted), and revoking access when they’re not.
Many organizations start with a zero-trust access product (e.g. for replacing or supplementing VPN) and then expand to segment internal apps and data. The goal is incremental: reduce the blast radius of a compromise and make every access decision auditable and policy-driven.
Myths and Realities
Zero-trust is sometimes sold as “no VPN” or “cloud-only,” but it’s broader than that. You can have zero-trust principles in a fully on-prem environment: identity-based access, segmentation, and assume-breach monitoring don’t require the cloud. Similarly, moving to the cloud doesn’t automatically make you zero-trust—if every cloud service trusts every user by default, you’ve just moved the castle. The key is consistent policy and verification, whether resources are on-prem, in the cloud, or hybrid. Another myth is that zero-trust is only for large enterprises. Small teams can adopt the same ideas: strong auth, least-privilege access to critical systems, and segmenting sensitive data. Start where the risk is highest and expand from there.
Why You’ll Need It
Regulators and insurers are increasingly expecting zero-trust or similar “never trust, always verify” postures. Remote and hybrid work have made perimeter-based security insufficient. And the cost of a breach—financial, reputational, and legal—makes the investment in identity-centric, least-privilege access a sensible default. You don’t have to do it all at once, but treating “zero-trust” as a direction rather than a checkbox will put you in a better position when the next incident happens. Zero-trust isn’t a silver bullet—but it’s the model that matches how we work and where our data lives now.






